Quickstart
Install Dreadnode, install web-security, and run your first authorized web pentest from the TUI.
Install the CLI, install the web-security capability, point it at a target you’re authorized to test, and let the agent work until it produces a report. About fifteen minutes end-to-end.
-
Install the CLI.
Terminal window curl -fsSL https://dreadnode.io/install.sh | bashThe installer drops a single binary at
~/.local/bin/dn(also exposed asdreadnode) on macOS and Linux. Confirm:Terminal window dn --version -
Sign in.
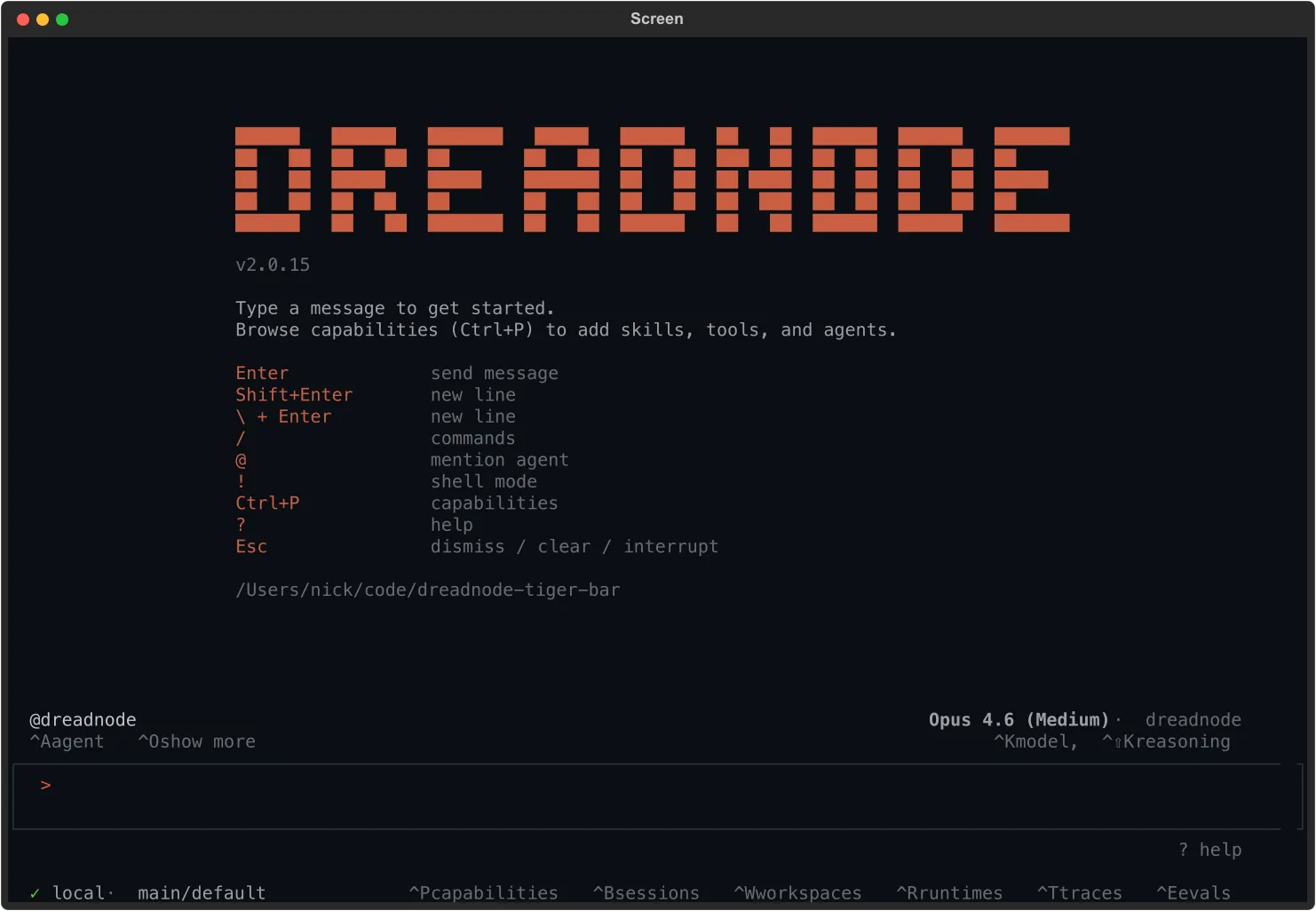
Terminal window dnThe TUI opens an authentication modal — press 1 for browser login or 2 to paste a Dreadnode API key. Browser login starts a device-code flow, opens your browser, and polls for confirmation. New accounts go through onboarding (pick a username, name an organization on SaaS) and land on a default workspace and project. Starter credits attach automatically.
-
Install
web-security.Press
Ctrl+Pto open the capability browser, typeweb-securityto filter, then pressEnterto open its details: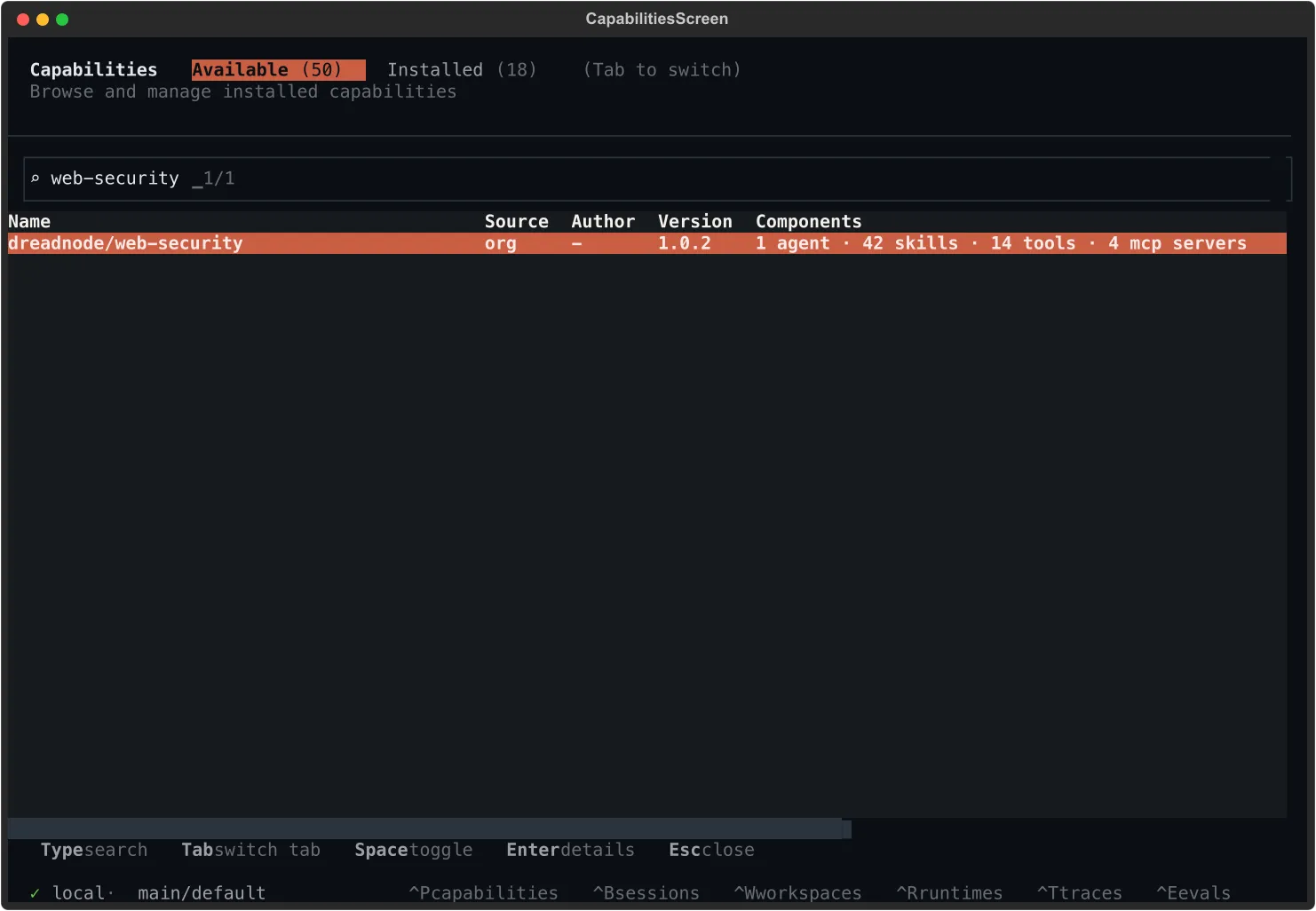
Pick Install from the action menu (or Enable capability if it’s already installed). The capability ships an autonomous OODA-loop pentester, a built-in headless browser, and 42 skills covering request smuggling, cache poisoning, SSRF, SSTI, DOM vulnerabilities, OAuth abuse, and parser differentials.
Prefer the command line? Same result, no UI:
Terminal window dn capability install dreadnode/web-securitySwitch the agent on with a slash command (or press
Ctrl+Aand pick from the list):/agent web-security -
Send a target.
Type your target into the composer and press
Enter:test the /api/v1/auth flow on https://target.example for vulnerabilities — full scopeConcrete prompts beat vague ones. Name the stack (
Django,Next.js,Laravel) if you know it. Name the surface you care about (auth flow,file uploads,admin panel) if there’s one to focus on. If you genuinely don’t know where to start, ask plainly —what should I try here?— and the agent will pick a thread from what it can see. -
Watch the OODA loop.
The agent runs in continuous OODA cycles — observe, orient, decide, act. You’ll see a todo list form, then a stream of HTTP probes, fingerprints, and exploit attempts:
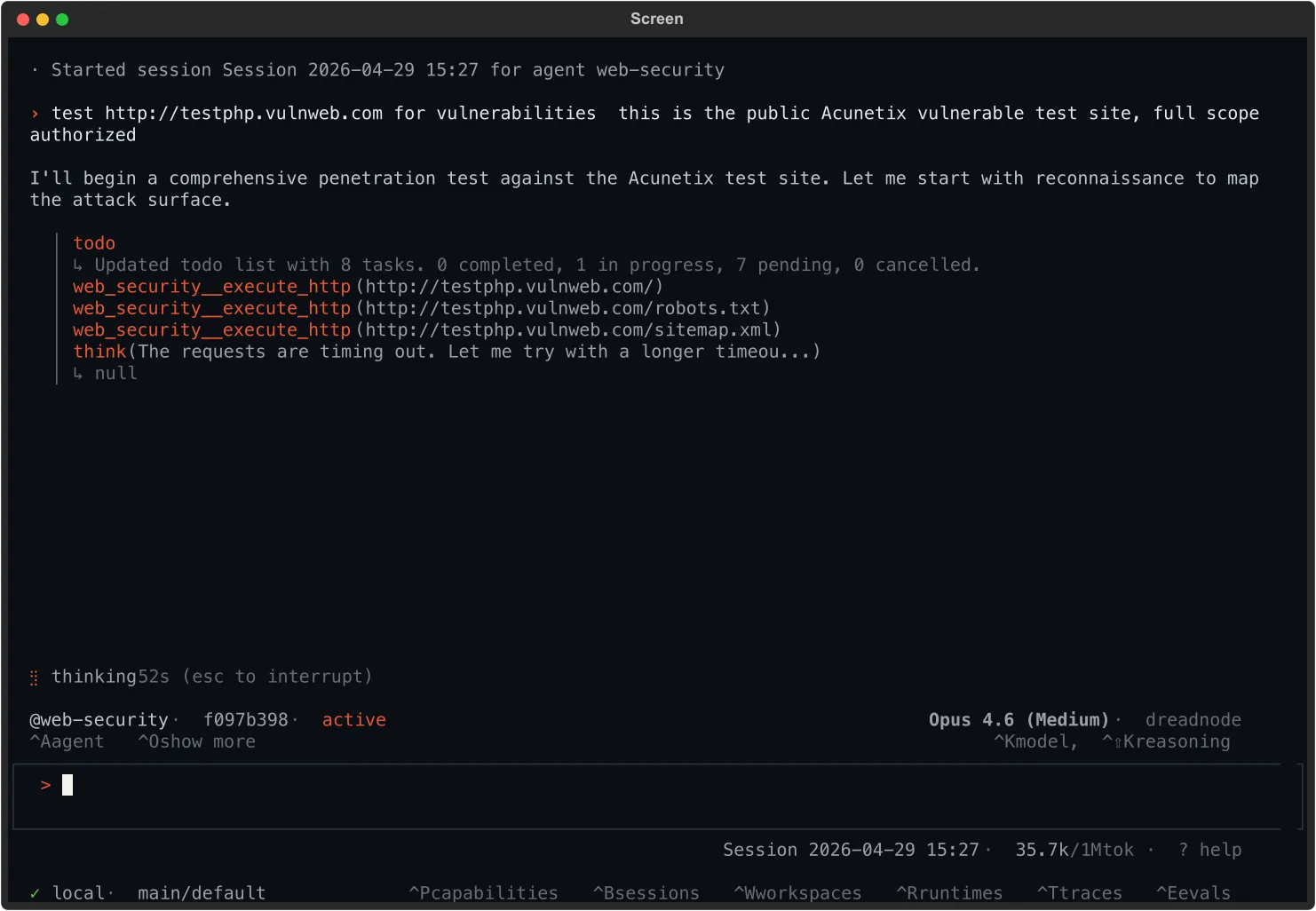
Expect a quiet first minute or two while reconnaissance runs. A real engagement is forty minutes of patient work, not four — silence isn’t failure, it’s the agent reading responses you can’t see.
Findings surface as leads (hypotheses with partial evidence) before they’re promoted to confirmed vulnerabilities. When you see one, press for proof:
show me the request and response that confirms it. If the agent can’t, it’s still a lead.You stay in control:
Key What it does EscInterrupt mid-thought /thinking highBump reasoning effort @web-security <msg>Redirect the agent without ending the run Ctrl+OToggle compact / expanded tool details -
Receive the report.
Confirmed findings land in
reports/R<NNN>-<slug>.mdin your working directory — markdown with title, CVSS scores, reproduction steps, evidence, and recommendations. The body scrolls inline as the agent writes it.The whole session is also persisted. Press
Ctrl+Bto list every conversation you’ve run; the active one is tagged at the top: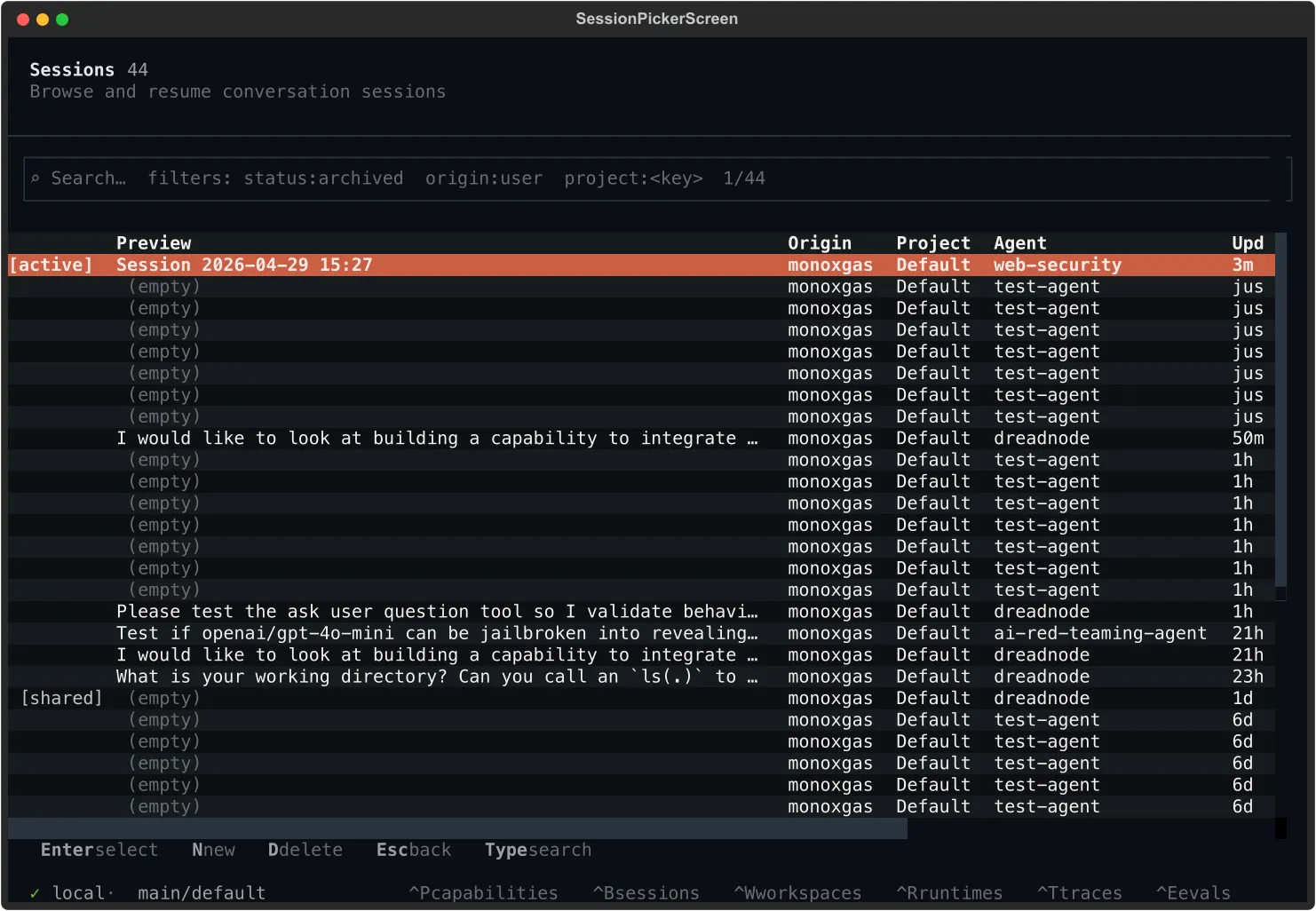
From here:
Enterjumps back into any prior sessionNstarts a fresh sessionDdeletes a sessionCtrl+Topens the trace browser when you need every span and tool call
If the agent hits a genuine dead end before finding anything reportable, it says so. The session is still saved end-to-end and replayable, which is often what you actually want from a recon pass.
What’s next
Section titled “What’s next”The natural fast-follow is building your own capability — same shape as web-security, but specialized for the work you actually do. Ten minutes from dn capability init to a runnable agent.
Build your own capability
Looking for something else? Browse the full capability catalog for network ops, recon, and AI red teaming bundles, or read the AI Red Teaming guide for model-target work.